Social Media Shenanigans: Dude in Rajasthan Busted for Fake Accounts

Suspicious friend requests? Your gut feeling might be right. A recent case in Rajasthan serves as a stark reminder to exercise caution when trusting individuals online, particularly on social media. A 22-year-old man was caught creating fake profiles of high-ranking police officials, including the Director of the Anti-Corruption Bureau (ACB), CV Anand. He reportedly used […]
Crypto Scam Alert: Gurugram Consultant Loses ₹38 Lakh in Deuncoin Fraud

A consultant in Gurugram fell victim to a cryptocurrency scam, losing a staggering ₹38 lakh (around $47,000 USD). While this story serves as an unfortunate reminder of the dangers lurking in the crypto world, it also offers valuable lessons for anyone considering crypto investments. Here’s how it unfolded: The consultant, whose identity remains confidential (a […]
Uh oh, Blackcat is Back! US Healthcare on Ransomware Watch

Heads up, healthcare heroes! The Blackcat ransomware gang is back in the news, and this time, they’re setting their sights on hospitals and other healthcare organizations across the US. Yikes! What’s the Blackcat Buzz? It is also known as ALPHV, is a group of cybercriminals who specialize in holding your data hostage. They do this […]
The Rise of a New Era: Hacktivism in the Digital Age

The rise of the internet has fundamentally reshaped the landscape of activism, fostering the emergence of hacktivism as a potent, yet contentious, force. This blog delves into the new age of hacktivism, exploring its evolving nature, impact, and the ethical considerations surrounding its practice. What is hacktivism? Hacktivism refers to the use of computer hacking […]
Cybercriminals Weaponizing Open-Source SSH-Snake Tool for Network Attacks

Have you heard about SSH-Snake? This open-source tool, originally designed for network mapping, has taken a dark turn. Cybercriminals are now weaponizing it to launch malicious attacks on unsuspecting networks. What is SSH-Snake? SSH-Snake is a network mapping tool that leverages SSH (Secure Shell) protocol to scan and discover devices within a network. While its […]
Average Breakout Time for Intrusive Activity is 62 minutes
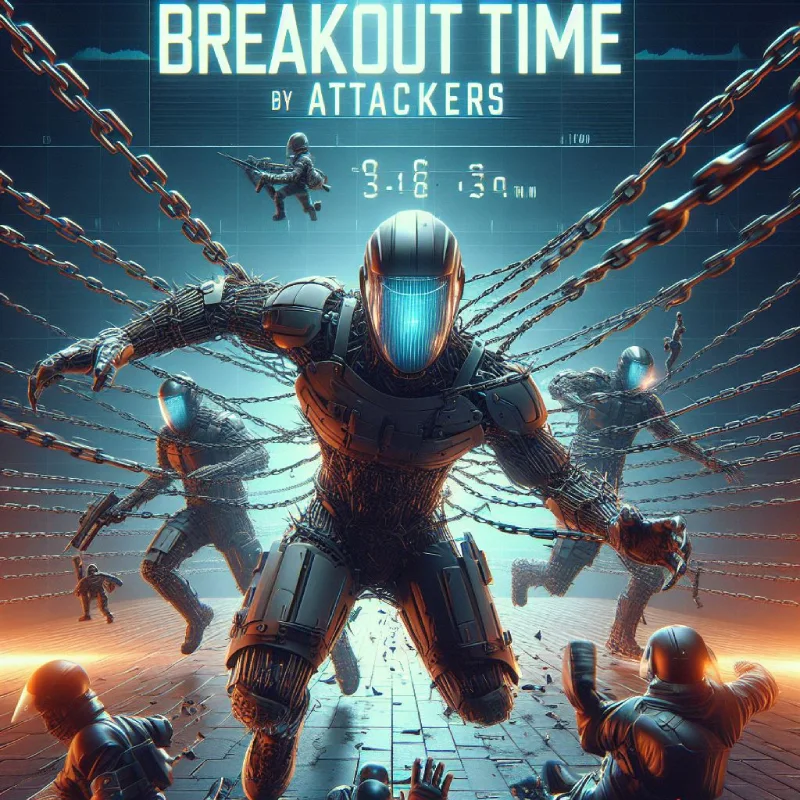
Learn what breakout time is and why its rapid decrease to 62 minutes is alarming for cybersecurity. Discover actionable steps to improve your organization’s security posture and minimize the risk of successful attacks. Stay informed and stay secure What is Breakout Time? Breakout time refers to the critical window between an attacker gaining initial access […]
Cyber Fraud Cases Skyrocket 200% in 2024: Are You Prepared?

According to recent data, cyber fraud cases have witnessed a staggering 200% increase in 2024 compared to the previous year. This alarming statistic highlights the growing threat that online scams and fraud pose to individuals and businesses alike. What’s driving the surge in Cyber fraud? Several factors contribute to this significant rise in cyber fraud […]
Beware! 8 Spyware Firms Are Targeting Your Devices

Spyware may be the reason you feel like someone’s monitoring your every online move. Meta, the tech giant responsible for Facebook and Instagram, has recently issued a warning about eight spyware firms that are targeting iOS, Android, and Windows devices. These companies specialize in creating and selling invasive software capable of pilfering your data, encompassing […]
Be Wary: Wiper-Ware Attacks on the Rise Amidst Geopolitical Tensions

Wiper-ware attacks, in a concerning trend, have seen a significant increase, as reported by cybersecurity firm Check Point, coinciding with heightened geopolitical uncertainty. Unlike traditional ransomware that seeks financial gain, wiper-ware aims to inflict maximum damage by permanently deleting data and crippling critical systems. This alarming development poses a serious threat to organizations across various […]
Is AnyDesk Safe? Understanding the Risks of Remote Access Tools and Phishing Attempts

Panicked call about needing AnyDesk to fix an issue with your bank, tech, or delivery? Don’t rush! It’s probably a phishing scam. Stay safe, learn more! These days, scammers aren’t just after your passwords. They want complete control of your device using tools like AnyDesk. Here’s how: 1. The Hook: Imagine getting a panicked message […]
